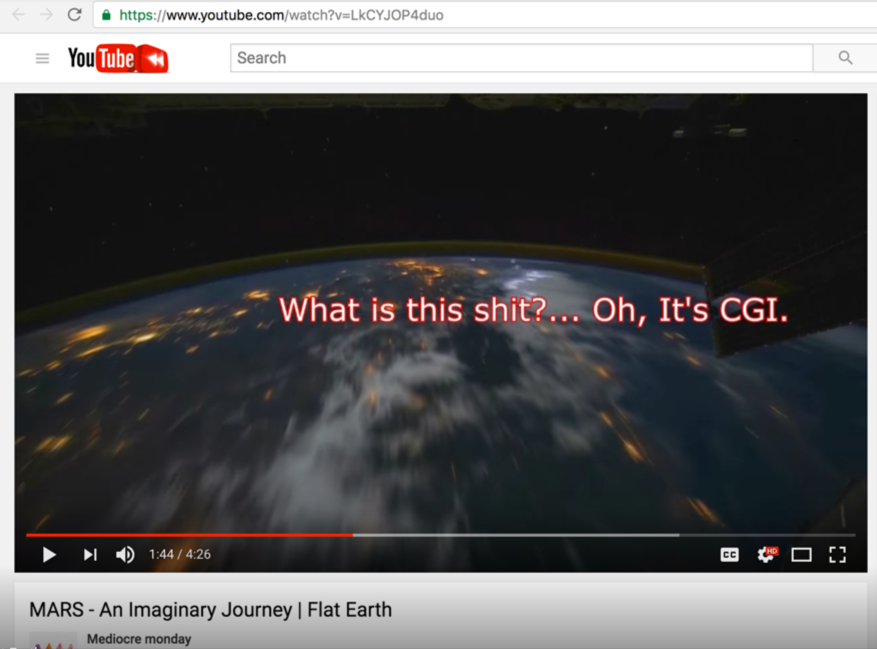
Mediocre monday (Wytse deJong) - MARS - An Imaginary Journey | Flat Earth
Dear Mediocre monday,
Fact check = You FAIL
Any idiot like you can make a claim, without providing proof.
So if this is CGI, put your money where your mouth is. Show us your photo forensic analysis proof.
(http://fotoforensics.com/)
With photo-forensics, you can test to verify if an image is pristine (never altered) or not.
That testing is done by analyzing the values of photo checksums created by analysis "Metadata."
In contrast to meta properties, cryptographic checksums (also called hashes or digests) act like digital fingerprints. It is extremely unlikely for two different files to have the same cryptographic checksum values. The most common cryptographic checksum algorithms are:
MD5: The Message-Digest Algorithm 5 (MD5) generates a 128-bit digest of the file. The hash is
typically written as 32 alphanumeric (hexidecimal) values.
SHA1: The Secure Hash Algorithm Version 1 (written SHA1 or SHA-1) is similar to MD5, but it
generates a 160-bit hash value. Compared to MD5, SHA1's longer hash size and alternate
computation method lowers the likelihood of a hash-collision, where two different files
generate the same hash value.
SHA256: The Secure Hash Algorithm Version 2 (SHA2) was designed to replace SHA1 due to
a theoretical mathematical weakness. Unlike SHA1, SHA2 defines a family of functions
that vary by bitsize: 224, 256, 384 or 512 bits. Each function is identified by the bit
length. For example, SHA256 is the 256-bit SHA2 hash function. Along with SHA2 is SHA3,
which defines even longer hash sizes.
OK?
Discussion at - https://www.youtube.com/channel/UC7ipUKERU0tzYFxALJBli4A/discussion
Video at..
(https://www.youtube.com/watch?v=LkCYJOP4duo)
kind regards, JonahTheScientist
- - - - - - - - - - - - - -
Show us the proof that confirms your claim that it's CGI...
- - - - - - - - - -